OCR-Quality® Risk Analysis

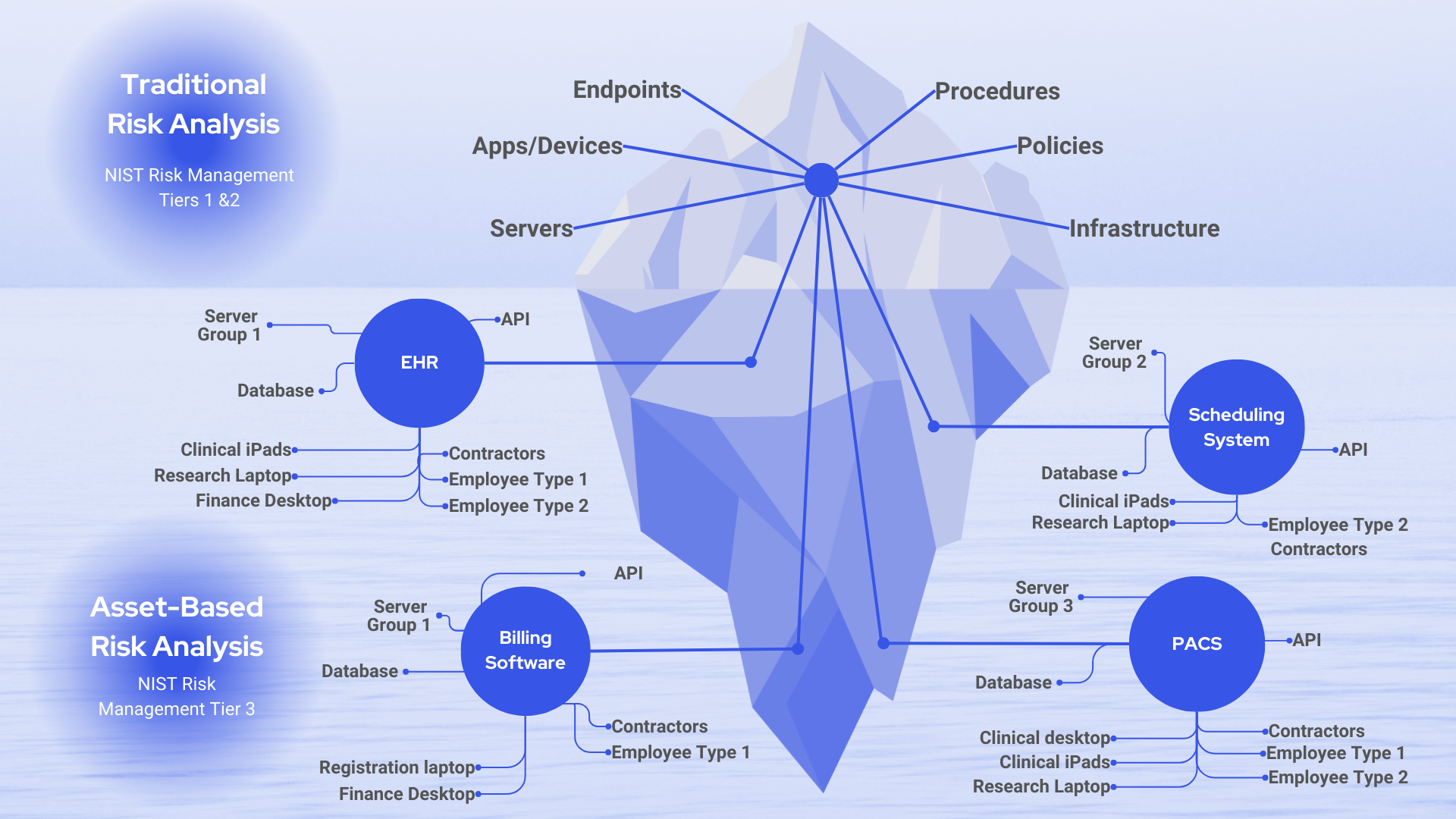
The one-size-fits-all approach to assessing cyber risk leaves a lot of questions unanswered.
Healthcare leaders are struggling to demonstrate risk reduction and program maturity despite completing assessment after assessment. This is because assessments only offer real value if they deliver actionable insights. If you stop assessing risk at the control level, you’ll miss the risks and vulnerabilities hiding among your organization’s component groups. Asset-based risk analysis doesn’t just check your compliance box; it equips you with insight and measurable risk data you can act on.
Asset-Based Risk Analysis Gives Healthcare Leaders
Precision & Confidence
Better visibility of your PHI and how it’s used and connected across your control groups means no more overlooked risks.
Successful Board Engagement
With a narrative that helps you demonstrate progress, you’ll be better equipped to engage your board and earn meaningful support from them.
Actionable Information
Meaningful data and analytics help you make better decisions and communicate more effectively.
Compliance Assurance
When you do risk analysis by the book, you’ll ensure your organization is protected and meet HIPAA requirements at the same time.
Risk Reduction
Leverage better cycle management to systematically reduce risk over time and never start from scratch again.
Cost Savings & Spending Power
When you can demonstrate risk reduction over time, you can justify the investment decisions you’ve made and advocate for new ones.
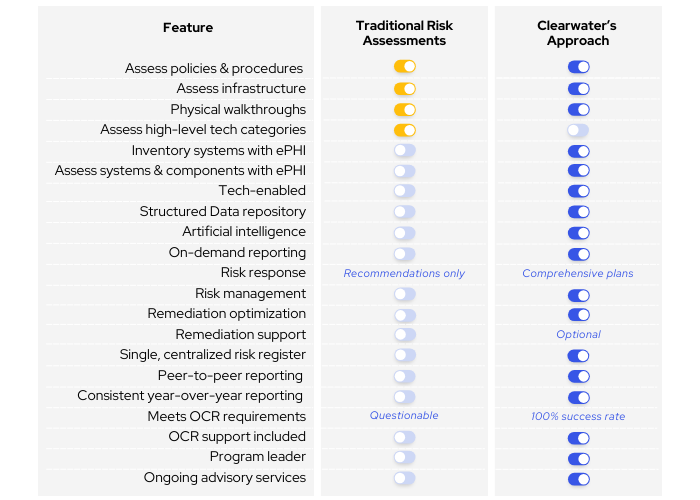
Traditional Risk Assessment vs. Clearwater’s OCR-Quality® Approach to Risk Analysis

The true risk assessment has made the biggest impact. Other companies give risk assessments, but Clearwater came in and did a very clearly laid-out job. (…) We have the best picture of our risk that we have had since I have been with the company. I presented the assessment to the board, but Clearwater gave me the materials that made the assessment understandable.
-KLAS Acquired Customer Comment
Why Clearwater?
The Clearwater team evaluates threats and vulnerabilities across applications, system components, cloud technologies, third parties, medical devices, locations, and even people, arming you with the security insights you need to determine the best path forward.
Get the clearest view possible of where your risks lie so you can tackle them head-on and stay in control of your business.
Want to Know More?

ClearConfidence™
Clearwater helps hospitals and health systems approach their cyber risk management programs with purpose and confidence through our ClearConfidence managed services program. ClearConfidence provides you with a dedicated team of cyber risk management experts you can trust to help you identify, prioritize, and manage cyber risk across your enterprise on a continuing basis.
We lay the foundation for best practices and help you maintain them while ensuring the right investments for minimizing cyber security risk.
Featured Resources
Connect
With Us



